Remote access never came closer to being a buzzword than in 2020. Of course, remote work has long been on the rise. But accelerated by social distancing, the number of permanent remote workers has continued to grow, and many are finding that outdated strategies for providing secure remote access aren’t up to the challenge.
Remote access challenges were (at least partially) responsible for 88% of hacking breaches and 95% of malware breaches even before the pandemic. The vulnerability caused by remote access is at least partially responsible for the 400% increase in cyber-attacks that was witnessed during the spring and summer of 2020.
Companies have a lot to consider when it comes to cyber in 2021. But top of that list should be building more sustainable security processes that can accommodate remote access flexibility. In the service of that goal, let’s go back and look at three questions you need to answer before supplying safe remote access to your system.
1. Who are your users and how many of them are there?
Not all users are the same, and they won’t all need the same kind of access. Providing one senior person or contractor with access to your system is a lot different than creating a standard process for 50% of your business. Blanket access solutions that use a one-size-fits-all approach to get up and running are faster to deploy, but deeply flawed.
High-level clearance across the board means that both internal and external breaches, when they happen, are sure to be severe. And, you might not even be able to work out where they originate! The focus on GDPR and other compliance regulations over recent years has especially thrown light on the need to limit information on a need-to-know basis.
From a security standpoint, understanding the ins and outs of your users, and limiting what they can do, brings a number of benefits, including:
- The chance to integrate tighter remote access cyber security;
- The ability to isolate and regulate access control;
- The opportunity to know who can gain access;
- A guaranteed way to monitor security/compliance from remote locations;
- The ability to minimise the potential impact of a breach.
Pro tip: When a team is working within one set office space, they’re all operating under the same regional regulations, but remote access throws that entirely up in the air. Not only does this pose security problems, but it also creates compliance concerns based on local data protection regulations. The IAPP’s handbook on data protection laws around the world is a good starting place if you have questions.
Strategies to help
You need a clear picture of who your users are, and the ability to provide user-specific access. There are two halves to this solution:
- Process: Understanding who your users are, and creating a set of default guidelines that align them with the information they need to get the job done without exposing unnecessary data and applications to risk.
- Technology: The ability to create different tiers of remote access permissions, and then easily switch between levels of access on a user-specific basis, as well as create exceptions to those rules.
The technology side of the equation will vary based on your overarching security apparatus. Most remote access servers, for example, will let you create pre-set permissions, and then assign them to users — and a managed service provider can help you execute such a strategy. But you need to understand who your users are and what they need to access in order to get the job done.
Key takeaway: Remote access relies on your ability to know and monitor users and their access. Rather than blanket solutions, a specific and segmented system approach that’s under constant review is fundamental for security and more.
2. What data and applications are being accessed?
If users aren’t created equal, then data definitely isn’t. To return to that point about GDPR — it’s often the data on offer, rather than your users, that poses access problems. Certainly, where external breaches are concerned, unchecked access to sensitive data causes the most significant issues, hence, why compliance has become such a pressing business concern.
While companies have spent a long time securing in-house systems, the broad scope of data access now poses issues that companies haven’t dealt with previously. In many ways, you could say that we’re all beginners again in the data safety sector. But asking questions here early may save you from upcoming struggles.
Strategies to help
The business world has been gearing up for remote data sharing for some time, with around 85% of companies turning to systems they feel they can trust, such as cloud computing. The solutions are there, and they’re already fine-tuned, but a little data awareness is necessary to ensure you implement a secure solution that fits. You simply need to consider data and application fundamentals, such as:
- What access does each team member need?
- What data should you be protecting?
- What security do you need in place to achieve that?
- How can you remain data compliant across locations without complicating your entire remote access system?
A cyber security risk assessment is the central tool at your disposal for determining the right answers to these questions and aligning them with your appetite for risk — ensuring the right level of access at the right level of risk.
Key takeaway: It’s essential that you understand what’s happening with your data. Only once you know this can you begin to work towards remote access that doesn’t leave your information open in unexpected ways.
3. What devices are your team using, and who owns them?
Once you know who’s accessing your system, it’s time to consider devices. The use of BYOD (Bring Your Own Device) is on the rise. Although BYOD brings benefits, it also creates significant security vulnerabilities. According to the Digital Guardian:
- 40% of large data breaches trace back to a lost or stolen device.
- 50% of companies that allow BYOD have experienced a breach via an employee-owned device.
- 65% of companies don’t have the ability to wipe devices remotely.
Ultimately, employee-owned devices raise a lot of question marks:
- How often is the device updated?
- What security systems are in place on the device?
- What other applications or software are on the device?
You could provide each team member with a take-home work desktop that enables remote access from a device that you control. But there are large out of pocket expenses and this approach, and it limits flexibility. Arguably, such extreme measures simply aren’t necessary.
Strategies to help
If you can create a system able to safely manage BYOD, you will have a solution that is really ready for flexible remote access. Again, this comes down to weighing up both technology and processes against risk. However, the basics of your security system can significantly impact the trade offs you need to make.
Our suggestion for device flexibility is endpoint security combined with managed detection and response (MDR).
- Endpoint security is a security approach that focuses on end user devices (or endpoints), but prioritises protecting the system as a whole, rather than each individual endpoint. This removes the need to focus on user device system updates, and allows you to control the entire security apparatus remotely.
- MDR closes the loop and provides active protection to threats flagged by an endpoint system, allowing your teams to mitigate an incident before it develops into a breach. This capability can be deployed in house, but is more efficiently delivered as a service — see, Four Way Strategic Partnerships Improve Cyber Security.
Although endpoint security and MDR are only one way to approach remote access, they provide a flexible foundation that will make large elements of your overarching security system far easier to manage.
Key takeaway: User-owned devices complicate remote access. However, building a system able to accommodate BYOD will help you create a flexible framework that will make providing remote access far simpler to safely accomplish.
Suggested reading: For more advice about MDR and endpoint security, check out our article — How to Build a Better Cyber Security System Today.
Building a more flexible and secure future
Cyber security isn’t a destination, it’s a journey. The threat landscape is always changing, and best practices need to change with the times. Creating a more flexible framework is key to solving problems of remote access. It will also help you create a system able to accommodate change and update quickly to remain secure — while doing more with less.
You needn’t overhaul your entire remote system to make this work. Instead, the how-to’s of building a more secure future are simple, and they include:
- Understanding your remote landscape from every possible angle including data access, device usage, and more.
- Considering what you need to keep safe, and who within your organisation needs access to what information.
- Seeking assistance to implement endpoint and MDR solutions that provide a long-term and flexible solution.
- Accepting that security is an ongoing process rather than a one-time issue, and continually adapting to your remote needs.
At Six Degrees, we’ve developed an iterative approach to cyber security assessments that we call the cyber security journey. It’s a continual security loop that allows you to scan your internal and external processes while also reframing your business strategy to support your existing team and their access needs.
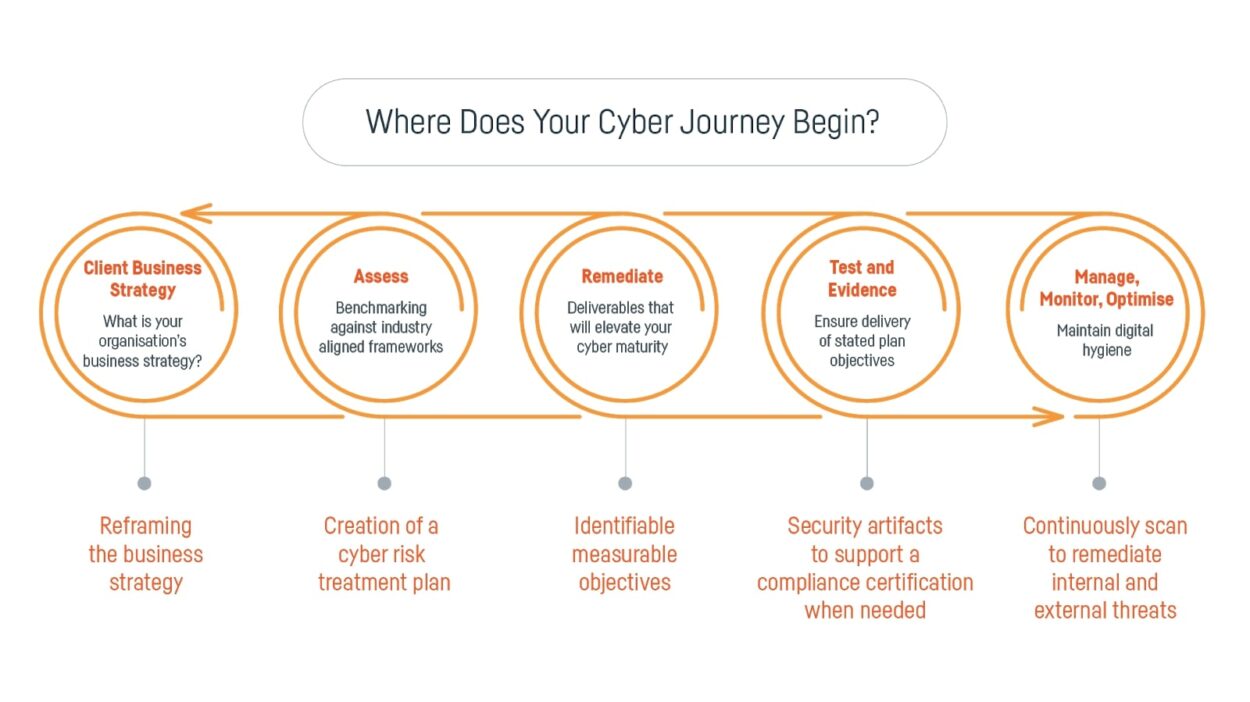
By changing your mindset to an iterative and flexible approach, you can lay the groundwork for more flexible access to your critical business applications and data. Long-term, this will not only create a more agile security system, it will make change like remote access far easier to accommodate. Then, you just need to make sure that the rest of your organisation is on board.
If you want to learn more about how to talk about cyber security within your organisation, check out our free resource — Board Presentation Toolkit: Cyber Security and Threat Management.
Subscribe to the newsletter today
Related posts
Your Five-Year Plan is Broken: Why 2026…
AI use skyrocketing, rising costs, global uncertainty, and…
From Defence to Strategic Advantage: Five Steps…
Resilience is often treated as a defensive capability…
Private Cloud is Back on the Strategic…
Public cloud remains powerful, but rising costs, FinOps…
Leadership, Strategy and Mindset: Making Resilience a…
In an era of constant disruption, resilience can…