Cyber security risk assessments sit at the heart of any effective cyber security strategy. They are about understanding, managing, prioritising and mitigating cyber risks within your organisation.
Fundamentally, a risk assessment requires answering questions like:
- What are your most important IT assets?
- How do you collect and store data
- What are your internal and external vulnerabilities?
- What is the likelihood that you suffer a cyber-attack?
- How would a data breach or cyber-attack impact your business?
- What cyber risks pose a threat to your organisation’s ability to continue functioning?
- What level of risk is your organisation willing to take?
By answering these questions, you can develop a strategy for action. Remember, cyber security isn’t about guarantees — it’s about priorities and informed choices. A risk assessment is about identifying those priorities and putting risk in context.
In this article, we are going to explain how to build a framework that will allow you to systematically ask the right questions about your organisation and understand the risks your face.
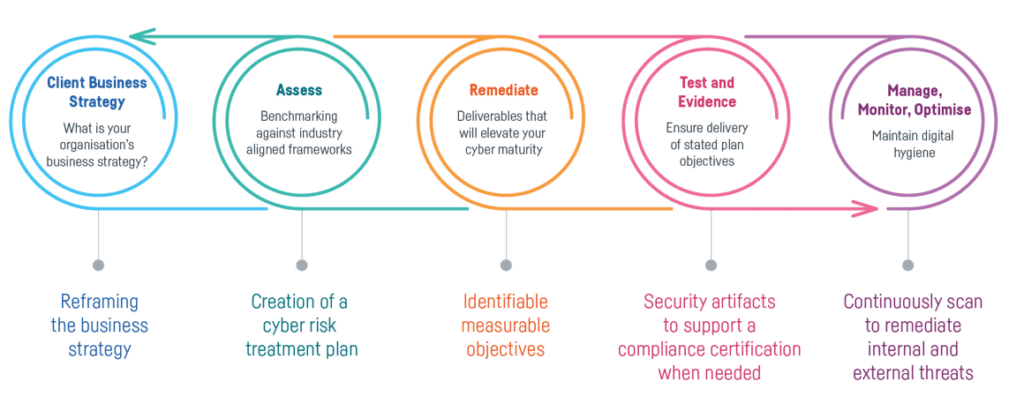
With that said, it’s important to remember that a cyber risk assessment is part of a wider cyber journey. That journey requires assessing risk, but it also means developing solutions, testing outcomes and monitoring progress in a continuous feed-back loop. “Cyber security” isn’t a destination, it’s a process.
At Six Degrees, we can take you through the risk assessment process and help you contextualise it within your cyber journey. For more information on that, and the critical process of presenting your finding to leadership, check out our free resources — The Board Presentation ToolKit: Cyber Security and Risk Management.
Step 1: Define your parameters and assess your assets
Not all risk assessments are undertaken for the same reason. The first thing you need to do is take stock of what you are analysing and why. This is about defining the scope and purpose of your assessment — including determining which assets you’re going to be assessing.
This is an especially important part of the risk management process within large organisations that have a large number of assets, personnel and process. Do your due diligence and prioritise your assessment to develop a cost-effective plan.
How to define the scope of your assessment
The scope of your assessment will look slightly different depending on your business and its goals. But at a high level, any business undergoing a cyber risk assessment will want to answer the following questions to determine scope:
- Is there a specific reason this risk assessment is taking place? What are you hoping to gain by doing this assessment? What outcomes are you after?
- What do I need to access in the organisation to get the information I need? Make sure you can access everything you need in order for the assessment to run smoothly.
- Are there constraints or priorities that may impact the outcome? Basically, is there anything you won’t have access to or operational activities that may be interrupted by the assessment?
- What data do we collect, how is it stored? This is different for every business, as are the risks associated with a breach.
- What does our IT infrastructure look like? Map out where your relevant assets are and how to access them.
- What existing systems are in place to mitigate risk? This is about understanding your present state so you can easily identify gaps.
Step 2: Identify threats
Once you’ve determined the scope of your assessment, the next step is identifying any threats to the security of your data. We define a threat as any instance where your data could be compromised with negative consequences. That could include:
- Malware
- Hackers
- Natural disasters
- System failure
- Human error
- Risks to third party vendors
This list is far from exhaustive. Depending on your business and industry, there may be other cyber threats that exist. It’s critical that you get a little creative in this step and think outside-the-box.
How to identify threats
At this stage, identifying threats is more of a brainstorming exercise than anything else (we’ll identify risk in the next step). And we always recommend starting threat identification as a team, where you can collectively bounce ideas off each other and everyone can contribute from their own perspective.
This helps you identify potential security gaps that you might otherwise miss individually when you’re assessing your systems and process. However, if you’re struggling to create a comprehensive list, our specialists can provide an outside perspective and help drill down on the critical threats to your business.
Step 3: Put those threats in context
Once you’ve developed a list of potential threats, the next step is to take your hypothetical threats and compare them against your actual systems and processes to determine their impact and the likelihood that they would actually occur.
We call those threats that have a high probability of occurring with negative consequences vulnerabilities. Vulnerabilities typically come in two forms:
- Systemic vulnerabilities. These are gaps in your security and information systems that hackers or malware could exploit intentionally to access sensitive data.
- Environmental vulnerabilities. These are internal and external gaps in your cyber security that could unintentionally or accidentally compromise your data (natural disaster, human error, etc.)
There are several ways to identify vulnerabilities in each category as you’re doing your assessment.
How to identify systemic vulnerabilities
Let’s address systemic vulnerabilities first. Typically, these will be identified through penetration testing, or intentionally trying to exploit your technical systems to gain access and find potential gaps.
However, it’s important to note that running an effective penetration test is as much an art as a science.
Just like identifying threats, penetration tests require experience and outside-the-box thinking to identify all of the potential ways your data could be maliciously accessed. So it’s critical that your tests are done by experts who are up to date on all of the ways that your security controls could be compromised (this changes quickly in today’s world). Get in touch if you want penetration testing help.
Otherwise, your risk analysis may not be as revealing as you want it to be and sensitive information could still be vulnerable.
How to identify environmental vulnerabilities
Studies show that human error accounts for almost 90% of data breaches. So you’ll want to be extra diligent with regards to identifying environmental vulnerabilities.
These vulnerabilities could include negligence on the part of your employees (leaving a laptop open in public or having it stolen all together), or policies around how data is accessed (can data be downloaded onto a zip drive and taken home?).
You’ll also want to review any changes in the cyber environment as they pertain to your industry during this step as well.
A good place to start with this is the National Institute for Standards and Technology (NIST) vulnerability database. This lists any reported vulnerabilities by month and year and will help you stay up to date with new risks.
Suggested reading: We regularly publish cyber-threat analysis reports.
Cyber Threat Intelligence Overview
CNS Cyber Intelligence Report: Trends in Ransomware Attacks against Legal and Accountancy Sector
CNS Cyber Intelligence Report: Threats to UK Financial Services
Step 4: Prioritise risks and actions
Once you’ve identified all of your vulnerabilities, the next step is determining which ones present the greatest risk and what actions you should take to mitigate them.
Fundamentally, there is almost always a cost associated with addressing vulnerabilities. So you need to weigh the cost of preventing that vulnerability against the cost of failure and the likelihood of failure.
When considering damage, think both long-term and short-term. For example, an immediate inability to continue business operations, or fines/lawsuits that may be likely. Long-term, do not underestimate potential reputational damage — something that is not always readily quantifiable, but often more financially impactful in the long run.
How to rank vulnerabilities
Here are a few questions to get you thinking about which vulnerabilities require action and when:
- What is the inherent risk to those assets that are vulnerable?
- What about those assets (information, data, IT infrastructure) is critical to your business?
- Which data would compromise your customers or partners if it were to be exposed?
- What regulations exist around the different types of data you store?
- Are there any fines associated with those regulations?
- How competitive is your market, and how are customers likely to respond to a breach or temporary suspension of services.
- What is your organisation’s stance on risk?
From there, it’s a simple matter of building a scorecard that ranks each vulnerability on a scale of low, medium, or high (you don’t have to be scientific about this — just as long as everyone in your organisation is on the same page).
Step 5: Record and present your findings
The goal of any assessment is to produce a report that records your findings and makes suggestions about actions in a clear and concise way (so that your board can understand why it’s worth spending to address, for instance).
In that respect, we find it’s always best to present the action in the context of damaged businesses outcomes if no action is taken, and the opportunities that effective action will open if taken.
If you need help with this, we’ve produced a board presentation template to help cyber security managers and leaders demonstrate the value of cyber to their board of directors.
Additionally, if you need help identifying potential risks to your organisation, we’re here to help. Our penetration test teams are some of the most highly regarded in the industry and we’d be happy to help you find and contextualise any risks your organisation may be facing. We can then construct an ongoing framework that will let you continue to improve the safety and security of your organisation.
Remember: this risk assessment is just a starting point for your cyber security journey. You need to use the information you uncover to feed an ongoing process that will help you maintain a secure outcome every step of the way.
Changes to the way we work are creating new uncertainties and opportunities. By sharing information and strategic choices, we can make a safer cyber-community overall. Good luck, and start assessing.
Subscribe to the newsletter today
Related posts
Your Five-Year Plan is Broken: Why 2026 Is Forcing a Cloud Reset
AI use skyrocketing, rising costs, global uncertainty, and increasing regulatory…
From Defence to Strategic Advantage: Five Steps to Turn Business Resilience into Growth
Resilience is often treated as a defensive capability focused on…
Private Cloud is Back on the Strategic Agenda in 2026
Public cloud remains powerful, but rising costs, FinOps pressures, and…
Leadership, Strategy and Mindset: Making Resilience a Strategic Imperative
In an era of constant disruption, resilience can no longer…






