In 2016, the UK government launched its five-year National Cyber Security Strategy (NCSS), following a spate of high-profile international cyber-espionage, cyber-terrorist and criminal attacks.
These included the 2009 breach of Google’s corporate servers by Chinese hackers, the 2014 Office of Personnel Management data breach and the Russian-sponsored attacks on the Democratic National Conference (both in the US).
Although Britain had not yet experienced a high-level cyber-attack, it was felt necessary to prepare for such an eventuality, as well as leveraging Britain’s leadership role in information technologies to drive innovative solutions to a growing global threat.
The end product of such concerns was the 2016 National Cyber Security Strategy (NCSS), which aimed to set out a roadmap for ramping up national cyber security over the following five years.
What is the National Cyber Security Strategy (NCSS)?
The NCSS is a government-initiated £1.9 billion programme of reinforcement of Britain’s cyber security infrastructure, knowledge base and methodology. During its first phase running from 2016 to 2021, the Strategy had a wide-ranging set of objectives. These included:
- Policy development and national uptake of cyber security measures
- A focus on cyber security education, to address a cyber security skill shortage
- Increasing investment in research and development
- International collaboration in cyber security data sharing
- Establishment of a National Cyber Security Centre
It was an ambitious set of objectives, and the NCSS may have suffered by trying to be too many things to too many stakeholders. But it has been the guiding force behind UK cyber security policy since its inception, and is important to understand if you want to plan for future change.
What the Strategy Got Right
As it draws to a close, the NCSS has achieved some of its objectives, at least in part. In perhaps its most significant move, it established the National Cyber Security Centre, now a fully integrated government department operating on four fronts:
- Providing practical guidance for non-expert managers and executives, on how to establish and adopt a meaningful cyber security strategy.
- Responding quickly to incidents affecting UK organisations and the wider public.
- Working with academic and industry experts to improve the UK’s cyber security capability.
- Reducing risk to UK governmental and infrastructural organisations across the private and public sectors.
In carrying out these four responsibilities, the NCSC will drive forward the most practical of the NCSS’s aims beyond 2022, as well as becoming an advisory body to the government.
Education, Research and Development
The NCSS also made inroads in addressing the lack of properly qualified and knowledgeable cyber security professionals. Between 2017 and 2019 the cyber security industry experienced remarkable growth, with a 37% increase in employment (from 31,000 individuals to 43,000) as depicted in the NCSS’s 2019 Progress Report. Despite this, however, there remains a cyber security skills gap that organisations of all kinds are struggling to fill.
In 2016 the National Cyber Security Programme included £10 million funding for a Cyber Innovation Fund, £13.5 million for the establishment of a Cyber Innovation Centre, and a Cyber Security Skills Immediate Impact Fund which, as of 2018, was training 170 key individuals.
Regional innovation centres were opened in Cheltenham and London to act as incubators for start-ups in the sector. Further work has been spearheaded to encourage school kids to study cyber security, including the enrolment of over 12,000 students aged 13-18 in a Virtual Cyber School in 2019-20.
These are all good initiatives, and they will pay off over the next decade or more. In the meantime, UK private and public sector organisations will need to find support in other ways — for example, by harnessing the support of managed cyber security specialists that can provide skills on-demand.
The Impetus for Change
In 2019, midway through its lifespan, a damning Public Accounts Committee report revealed that, thus far, the Strategy had only achieved one of its targets (incident management). Although there is a lot to like regarding the NCSS, its broad-reaching objectives have made it difficult to achieve any of them fully. Then, in 2020-21, the largely unforeseeable COVID-19 pandemic accelerated public dependence on IT solutions for work, entertainment, communication, and education, shifting the focus somewhat onto end-user risk management strategies.
The pandemic also underlined the vital importance of cyber security, as it demonstrated our global reliance on information technology and our vulnerability to its being compromised — trends that were already underway. 2017’s WannaCry ransomware attack and the March 2020 breach of the WHO made headline news and provided ample reinforcement of the timely need for a robust national cyber strategy. It seemed that a war was being waged on three fronts — against cybercriminals, cyber-terrorists, and hostile nations.
Over in the US, it became evident in 2020 that potential espionage from global superpowers was perceived to be a significant threat to the US’ cyber sovereignty. The Trump administration’s sanctions on Huawei made it impossible for the Chinese tech provider to use US-manufactured components in their systems. The NCSC analysed the impact this would have on the UK’s national roll-out of the Huawei-powered 5G network. In its report to GCHQ, it concluded that Britain could no longer reliably ensure the cyber security of the network if Huawei was involved.
When the government pulled the plug on UK telecom companies using Huawei 5G technology, the world had a vivid demonstration of the risk of global technology collaboration in an era of geopolitical instability. This decision may have lost the UK some face, it’s true. However, the potential danger of exposing our communication networks to a potentially hostile superpower left the government with no choice. The NCSC’s report made a difficult decision easier to make.
What Does the Future Hold?
In order to build on the modest successes of the NCSS in the coming decade, what should the priorities be?
In 2019, independent defence and security think-tank RUSI (the Royal United Services Institute) put together a research project to determine the best course for national cyber security beyond 2021. It asked what was more desirable — the likely mainstreaming of cyber security within UK government departments, or the continuation of the NCSC and its arm’s length approach.
Their 2019 briefing paper identified some likely trends:
- That involvement of the private sector in ongoing national strategies is desirable, and that this will necessitate a whole of society approach.
- That core internet security will be key and initiatives like the NCSC’s Active Cyber Defence programme could help instil good practice beyond the private sector.
- Vulnerabilities in the Internet of Things (IoT) need to be identified and eradicated, since this is a notable weak spot in overall cyber security provision.
- Bad actors will continue to become more sophisticated in phishing attacks, necessitating improved multi-factor identification and cyber-hygiene education within the general public.
A key theme overall in the briefing paper is the need for an enhanced role for private sector providers partnering with the public sector and government. As the paper notes “There must be a clear mutual understanding as to where UK government responsibility ends, and private sector accountability begins. This dialogue is at present only in the early stages.”
RUSI does not anticipate there being as big an investment in national cyber programmes in 2021 as there was in 2016, in part due to the debt burden occasioned by the pandemic. It’s not yet clear whether the UK government plans to renew the NCSS, but we should anticipate news soon, and expect at least some of its more vital components to continue.
Reducing Corporate and State Vulnerabilities
If the 2020-21 COVID-19 global pandemic has demonstrated anything, it’s how reliant we all are on the technologies we hold in our hands and use in our work, as well as how open even the biggest private sector companies or superpowers are to attack. Cyber-crime alone is predicted to cost the global economy $10.5 trillion by 2025, and remote working has created new cyber security vulnerabilities that need to be taken seriously.
No amount of investment in protecting our public sector from these threats will solve the problem of hackers or foreign agents infiltrating the data held by private sector companies such as Google, Microsoft, or Facebook, not to mention the tens of thousands of business tools we all employ daily, including cloud storage, email services and e-commerce portals.
European and UK GDPR legislation went some way to enforcing a standard for data protection. However, cyber security protocols are a lot more variable, and hidden vulnerabilities are everywhere. How do you assure your clients that their data is safe and that your servers are protected from attack? At Six Degrees, we believe the answer comes down to different ways in which cyber security is approached, and how resources are allocated.
Cyber Security as a Journey
A key lesson for any organisation coming to terms with cyber security threats is that you can never be 100% risk free. It’s important to build a cyber security process that takes this into account and is able to respond flexibly to changing circumstances. We’ve come to call this mindset the Cyber Security Journey.
At Six Degrees we offer managed security services, penetration testing and managed detection and response (MDR). Any organisation that comes to us for consulting services will be advised to think about cyber security as a circular process with stages including:
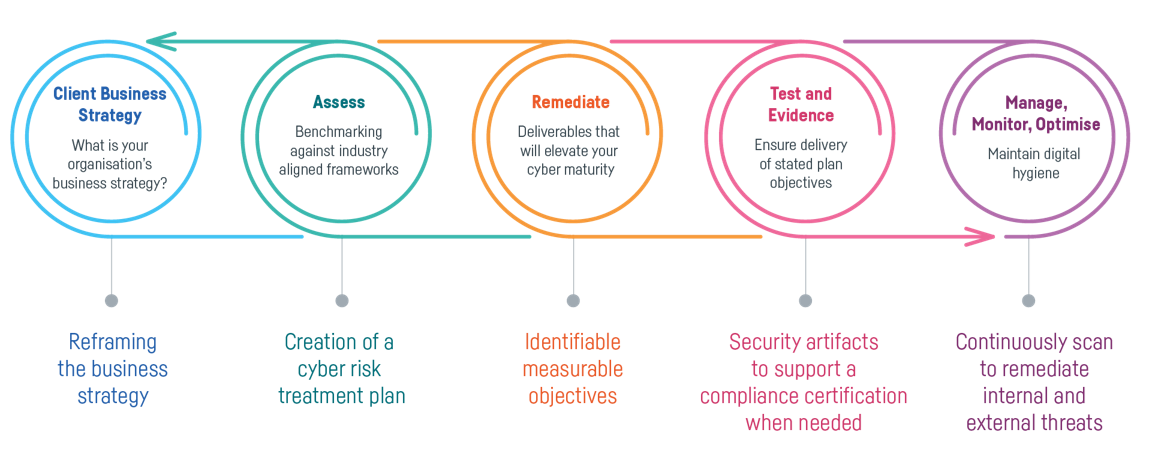
By moving through this process, you will be able to iteratively assess your vulnerabilities and develop more robust solutions based on in-life feedback and real-world results. Critically, you are able to keep your organisation secure without grinding operations to a halt. Long-term, we believe that integrating cyber security into your culture and taking an iterative approach is critical to match the challenges of the shifting threat landscape.
Get in touch if you want to learn more, or check out our free resource — Planning For the Future of Cyber Security Today.
Subscribe to the newsletter today
Related posts
Our New Pricing Tool Shows How Much…
Public cloud is not always the most cost-effective…
Your Five-Step Plan to Address Mythos Cyber…
Artificial intelligence is accelerating cyber threats at an…
AI in the Enterprise: Opportunity, Risk and…
Artificial intelligence has evolved at a pace few…
Your Five-Year Plan is Broken: Why 2026…
AI use skyrocketing, rising costs, global uncertainty, and…