The Cyber Essentials Standards have changed. Your organisation will need to adapt if it wants to remain aligned. In this blog our Technical Director – Offensive Security Andy Swift takes you through what you need to know.
The Cyber Essentials and Cyber Essentials Plus schemes have been running for several years, and although the recent updates have been relatively small, they are still very much worthy of noting.
Accreditation body IASME has been working on improvements for both standards since taking over sole responsibility for the delivery of the scheme, and the latest update that took place on 24th January 2022 marked the biggest change to the standards for a number of years. If you are new to the standard, you can get up to speed here.
The revised and improved standards are now live; I believe the updates are very much due, as they aim to maintain the goal of the scheme to raise the bar for security standards in business across the UK.
But what are the updates? And why should you start preparing now?
Why You Need to Adapt to the Updates
To answer the latter, the changes are mostly around scope. Traditionally where changes to scope have been introduced in the past (either by client request or enforced by changing standards) passing the standard becomes more complicated and time consuming at first. Preparation for these changes is going to be key to a smooth certification or recertification process, so it’s important they are both understood well ahead of time.
What Are the Cyber Essentials Standards Updates?
First off, there is an option for a sub-set of the network to be considered for accreditation. The interesting addition here is the definition for the term ‘sub-set’ to the standard which was much needed. The definition for sub-set is now “a part of the organisation whose network is segregated from the rest of the organisation by a firewall or VLAN. A sub-set can be used to define what is in scope or what is out of scope of Cyber Essentials. Use of individual firewall rules per device are no longer acceptable.”
The following graphic better describes what is typically considered in-scope for the majority of assessments:
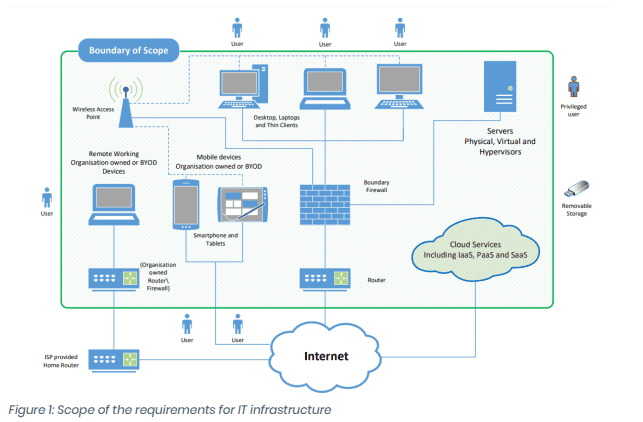
Source: https://www.ncsc.gov.uk/files/Cyber-Essentials-Requirements-for-Infrastructure-v3-0-January-2022.pdf
Home Working Devices
Working from home has really hit the mainstream over the last few years, helped nicely along by a global pandemic… With that, the growth in home working devices has been huge. I wrote an article not so long ago about how many teams struggled in the early stages to provide equipment at rapid demand while also keeping in line with their usual security standards; the truth of the matter is many have not, and the result is presenting attackers with some very wide attack surfaces indeed! This addition to scope aims to ensure such devices are under control.
Devices (personal or owned by the organisation) used by home workers to access corporate data are now deemed to be in scope for Cyber Essentials. Home routers are now out of scope; however, if the applicant company has provided routers to its users then these will still be considered in scope.
Cloud Services
All cloud services are now to be considered within scope of the scheme. If the organisation’s data is being stored or accessed via a cloud-based platform, the applicant organisation will be responsible for ensuring all Cyber Essentials controls are applied. Definitions have been provided for Infrastructure as a Service (IaaS), Platform as a Service (PaaS) and Software as a Service (SaaS); which of these types is involved will depend on who is responsible for enforcing the controls that are applied. The following table is taken from the NCSC’s ‘requirements for infrastructure’ documentation and outlines the responsibilities. The applicant will need to be confident and have agreements in place to ensure responsibilities of third parties meet that of the standard.
| Requirement | IaaS | PaaS | SaaS |
| Firewalls | Both applicant and cloud provider | Cloud provider and sometimes also the applicant | Cloud provider |
| Secure configuration | Both applicant and cloud provider | Both applicant and cloud provider | Both applicant and cloud provider |
| User access control | Applicant | Applicant | Applicant |
| Malware protection | Both applicant and cloud provider | Cloud provider and sometimes also the applicant | Cloud provider |
| Security update management | Both applicant and cloud provider | Both applicant and cloud provider | Cloud provider |
Multi-Factor Authentication
Multi-factor authentication (MFA) now needs to be applied to all cloud-based services. To start with this will apply to system administrators only, but over time will apply to the whole user base; in this case however we would recommend it being applied to the entire user base anyway. The number of attacks against cloud-based system users has grown hugely over the last few years and now represents one of the biggest and most fruitful attack vectors. Incident response cases attended by the Six Degrees Offensive Security team over the last year have in over 80% of cases been traced back to an initial entry via a system not using MFA. Using a secondary factor of authentication can help stop such attacks in their tracks, and this is something many system administrators refer to now as a non-negotiable.
Thin Clients, Servers and Virtual Servers
Thin clients that connect to organisational data are now also to be included within the scope of the Cyber Essentials assessment, alongside all servers (virtual or otherwise).
Mobile Devices
All mobile devices that connect to the organisation and can access organisational data are now in scope and must be protected using biometrics or a minimum 6 character pin.
Password and MFA Requirements
Password strength and MFA settings have been hot topics of discussion for several years outside of Cyber Essentials, and over time have seen a number of best practice revisions. For Cyber Essentials specifically the changes added to the new version of the standard are as follows.
Where passwords are in use anywhere within the scope, one of the following must be applied:
- The use and implementation of MFA
- Throttling the rate of unsuccessful attempts
- Locking of accounts after no more than 10 unsuccessful attempts
In terms of password strength, these too have had an overhaul and the following guidance has been provided; just note that only one of these options needs to be met:
- Using multi-factor authentication in conjunction with a password of at least 8 characters, with no maximum length restrictions
- A minimum password length of at least 12 characters, with no maximum length restrictions
- A minimum password length of at least 8 characters, with no maximum length restrictions and use automatic blocking of common passwords using a deny list
Account Separation
Account separation is an interesting addition to the standards, and it is geared towards ensuring administration accounts are used for just that – administration and administration alone. There should be no ‘standard’ user activities performed using administration accounts, and in particular they list web browsing and emailing as examples of such activities.
The Scope of an Organisation Must Include End User Devices
End user devices are now required to be in scope for any assessment. You can no longer just certify a collection of servers or a given ‘environment’ without including the end user devices that access or administrate them.
This is being seen as a positive step in the security world. Attacks don’t just originate within environments; often they are introduced by weaker connecting devices from users or even administrator devices.
14 Days to Apply High and Critical Updates
For all devices in scope, a 14-day period to apply and close High and Critical updates is mandated. These are issues described by the vendor as ‘Critical’ or ‘High’ severity, or hold a CVSSv3 score of 7 or above.
Many will likely see this change as one of the most challenging to overcome. It will require extra vigilance and coordination to maintain, yet at the same time it is very much required to improve the standard of cyber security within the UK.
There have been several high-profile vulnerabilities this year (Log4J for example) that have gone from disclosure to public knowledge to being weaponised in mere days; it is no longer viable (and arguably it never has been) to leave such issues exposed for more than 14 days while maintaining the standards of security.
How Will These Updates be Introduced?
Given how large some of these changes are, they are going to be introduced gradually from 24th January 2022 going through to January 2023. Most of them will appear within the questionnaires from 24th January 2022, but in specifics there are a few caveats; the MFA requirement for Administrators will kick in for 2022 while the requirement for MFA to be applied to all users will be moved further down the line to January 2023.
The same applies to the requirement to remove unsupported software; this will be marked in the questionnaire for compliance from January 2023, but for now will only be used as informational data during 2022.
For further questions or to begin the certification process with support and guidance from Six Degrees, feel free to contact us for quotations.
Subscribe to the newsletter today
Related posts
Cyber Security Maturity Assessment
Fortify your organisation’s security posture by evaluating your…
Planning for the Future of Cyber Security…
Planning for the Future of Cyber Security Today…




